'Anonymous': How dangerous is hacker network defending WikiLeaks?
Loading...
A self-styled and loosely affiliated group of Internet-freedom fighters dubbed “Anonymous” has morphed into a borderless digital militia, slinging Twitter posts and virtual handbills across cyberspace to coordinate digital attacks in defense of WikiLeaks and becoming a new force to be reckoned with on the Internet.
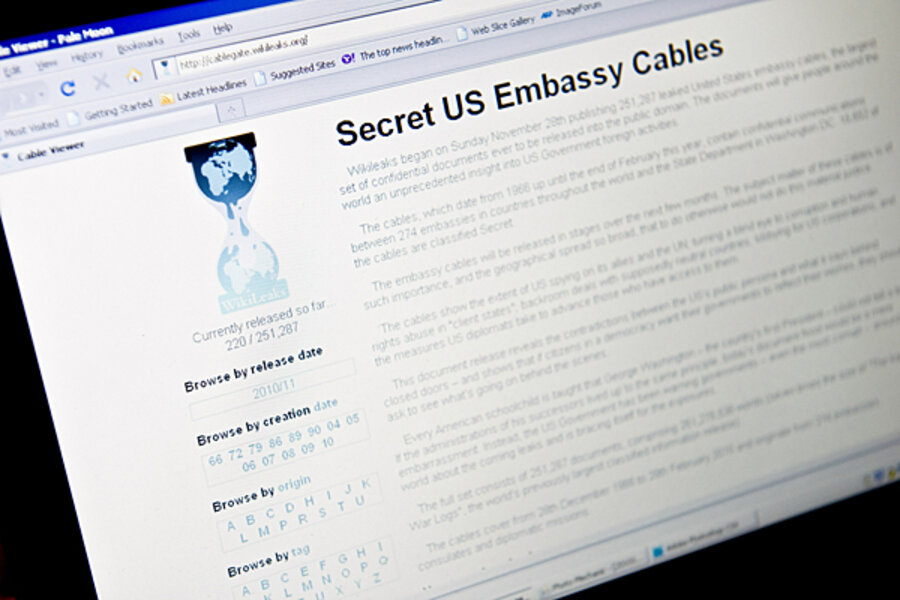
In the global furor since WikiLeaks' release of secret US documents and the arrest of the group's founder, Julian Assange, cyber attackers have crippled corporate websites. To do so they have deployed old digital weaponry forged by new social media tools into a novel virtual global attack system that is leaderless, anonymous and powerful.
"Operation Payback" is the name that Anonymous has given its cyber-retribution campaign against corporations that have withdrawn support and services from Mr. Assange, who was arrested in Britain in connection with a Swedish investigation into allegations of sexual assault. [Editor's note: The original mischaracterized the reasons for the British arrest.]
As of Thursday, the group's attacks had crippled or brought down with distributed denial of service (DDoS) attacks at least a half dozen major websites belonging to Visa, Mastercard, PayPal, the Swiss bank Postfinance and others that withdrew services to WikiLeaks.
"This is probably the largest attack of its kind," Derek Manky, an Internet security expert at Fortinet, a Sunnyvale, Calif., computer security company. "It's not just one specific audience trying to launch an attack. It's a much more global audience – a global group – and these targets that they're taking down are not small."
Large they may be, but DDoS attacks like those that hit Mastercard, Visa, Paypal and other corporate websites by flooding them with data and Internet requests are nothing new, or advanced, technically speaking. Such attacks involve creating or enlisting the support of botnets – many thousands of computers coopted to work in tandem – and getting several of them to focus on particular Internet sites to clog them by making virtual information requests simultaneously. A sort of cyber blockade.
Use of social media is key
But it is the use of social media and the novel way old digital attack weapons are being organized that experts say is at the heart of what's happening, say experts who have studied the group. Anonymous members have essentially posted virtual handbills across the Internet on websites and Internet relay chat forums to rally new participants.
"We will fire at anyone or anything that tries to censor WikiLeaks. … Twitter, you're next,” reads one such handbill circulated Monday prior to a second DDoS attack on Paypal, according to Panda Labs, an Internet security research firm.
There are signs that some of the social networking sites are responding. Facebook and Twitter Thursday morning were reported by Reuters to have deleted the accounts of cyber activists who targeted Visa and other Internet payment sites.
There have been patriotically motivated attacks in the past. After the US accidentally bombed the Chinese embassy in Belgrade in 1999, Chinese hacktivists posted messages on US government websites like “We won’t stop attacking until the war stops!” Russian hacktivists attacked Estonia after plans to move a Soviet era statue.
Yet Operation Payback's "anonymous" global call to action to avenge Mr. Assange and to keep WikiLeaks information flowing free onto the Internet, has resonated and apparently garnered considerable firepower from both individuals and botnet operators in a number of countries, say Internet security experts.
Operating on the model of inciting to action like-minded individuals – a so-called "hive mind" approach according to the group's literature – Anonymous has a track record of several years of Internet-based protest attacks and pranks on those it deems to have opposing values. Previous Anonymous targets include a white supremacist website, an alleged Internet child predator, YouTube, and the Church of Scientology, according to published reports and experts who have studied the group.
"This group has a history of tongue-in-cheek attacks and pranks," says Patrick Underwood, a University of Washington researcher on online communities including Anonymous. "It is called anonymous because it really is. You have a small group that communicates entirely anonymously. Someone basically says 'We should give this thing a name, make some flyers put up on the [Internet] bulletin board saying, 'This is what happened. We think it's wrong. If you want to do something come to this website and we'll do something about it.' "
Hacktivism – the use of nonviolent albeit illegal digital weapons toward political ends – is hardly new either. Nor is defacing websites, denial of service attacks, and the hacking and sabotage of computer systems – all things hacktivists specialize in doing.
"One thing that's new about the Anonymous group is that they're not a group in any formally designated sense," says Ted Welser, a sociologist at University of Ohio who studies online communities. "This is more of an amorphous community. They post comments on sites like 4-chan where anyone can show up. The handle is anonymous for everyone. It includes teens and older, hugely varied, people with some sort of technical skills, from college-age kids to 14-year-olds in their parents’ basement."
"If you go online and join in an operation and help the cause, if you act under the umbrella of Anonymous, or if you show up for an event, then you are 'Anonymous,' " says Gregg Housh, an unofficial spokesman for Anonymous and co-creator in 2008 of one of the Anonymous forums, WhyWeProtest.net.
By day he is a technician manager at Boston company Geek Choice. By night, he goes by the title of "activist associated with Anonymous." He is very careful to mention that he has not participated in any of the DDoS attacks.
A global mission
Anonymous activists are chatting back and forth on the Internet Relay Chat system, he says. At one point Wednesday, he says, everyone began saying hello from their respective country, giving a sense of the global nature of the mission.
"You saw this list of the world," Housh says. "Every continent but the frozen one seems to be in that channel."
But to some observers, however, what's happening with Operation Payback may be more about a growing mob or vigilante mentality on the Internet – even if it pulls in idealistic people with a notion that the Internet needs to be free.
Anonymous is urging others to join in taking action – without thinking too deeply about the ethics or consequences, say those who have observed the workings of the group on websites and chat forums.
"The people doing this say they're ticked off, that they want to do something, that these people are bad, so I'm going to do a DoS attack," says David Dittrich, an expert in denial of service attacks at the University of Washington. "But this is the way a mob operates. No way can it be ethically justified and it just feeds on itself through anger and agitation. It may be anonymous now – and it may get bigger – but it can't end well for people who do this. Someday they may kick the wrong hive."
Monitor staff writer Stephen Kurczy contributed to this article.