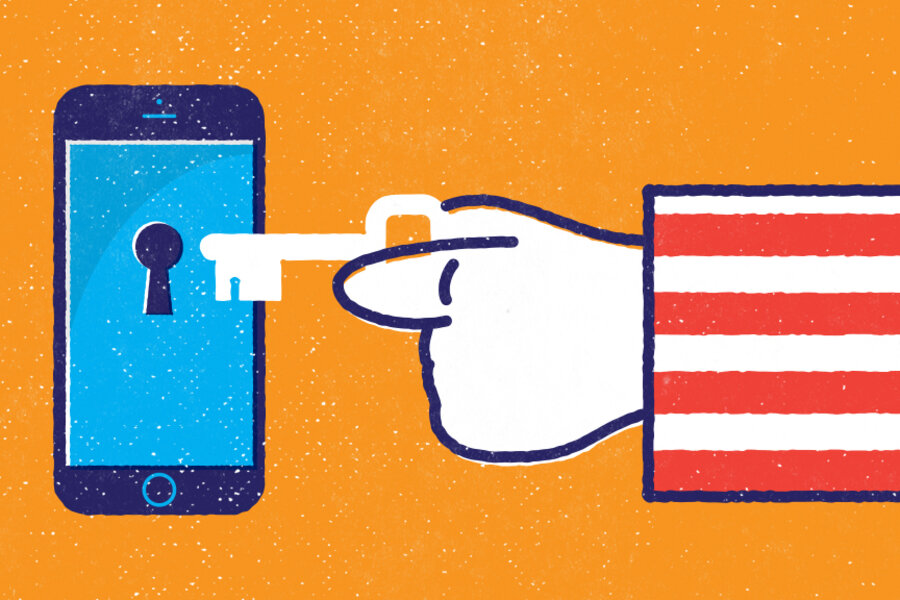
Opinion: Why we should not fear a world of ‘universal encryption’
Loading...
When it comes to cryptowars 2.0, the FBI still can’t admit that it’s on the wrong side of history.
Ever since Apple and Google announced last fall that new iPhone and Android phones would be encrypted by default, FBI Director James Comey has been complaining that the growing prevalence of encrypted devices and Internet services will prevent law enforcement from obtaining the data it needs for its investigations.
While it’s sparked a yearlong policy battle between Washington and Silicon Valley over encryption, Mr. Comey and his colleagues still have yet to reveal much in the way of concrete examples in which strong encryption is causing the kinds of problems that they fear – while there’s plenty of reason to think it will actually stop more crimes than it will shield from scrutiny.
To be honest, the crypto “debate” should not be much of a debate at this point. Just as they did during the cryptowars of the 1990s, a broad coalition of tech companies, privacy advocates, and security experts have made clear that the US government mandating that our digital products have built-in surveillance “backdoors” (or “front doors,” as Comey would prefer we call them) would be bad for cybersecurity, innovation, human rights, and the American economy. Even the White House seems to recognize that pushing for such a mandate is a bad idea.
But that hasn’t stopped Comey from painting an apocalyptic picture, in blog posts and in Congressional testimony, of a world of “universal strong encryption” where every bit of data is beyond the reach of the cops, and chaos reigns. “As all of our lives become digital, the logic of encryption is all of our lives will be covered by strong encryption,” he said in a speech earlier this year. “Therefore all of our lives … including the lives of criminals and terrorists and spies, will be in a place that is utterly unavailable to court-ordered process.”
Sounds scary, doesn’t it? Don’t be afraid, though. The “universal encryption” scare-story being sold by the FBI – where one day every communication will be secured by end-to-end encryption – isn’t going to happen anytime soon. And, ironically, it’s the FBI’s own latest argument in the encryption debate that demonstrates why it isn’t going to happen.
Comey floated this new argument at a cybersecurity hearing on Capitol Hill last week, responding to the chorus of security experts that have concluded that it’s not possible to engineer back doors for government surveillance of encrypted data without also diminishing security against other, less savory attackers.
In that hearing, Comey noted that plenty of Internet communications services don’t strongly encrypt all the way from the sender to the receiver (i.e., “end-to-end” encryption) as done by messaging services such as Facebook’s Whatsapp or Apple’s iMessage, but instead store in the cloud and maintain their own access to users’ data for business purposes, such as scanning e-mail contents to serve ads. Those companies, in turn, are able to respond to government demands for that data.
“I’ve never heard anybody say those companies are fundamentally insecure and fatally flawed from a security perspective,” Comey continued. The implicit message: If we all think that Gmail is secure enough, or Facebook private messages or Twitter direct messages, why can’t everyone just build their services that way?
By my count, FBI and Justice Department officials repeated some variation of this argument at least five times at an event on the encryption debate hosted by Passcode earlier this week.
As the Justice Department’s Kiran Raj, senior counsel to the deputy attorney general, argued there: “There are large companies, for example, some of the commercial e-mail providers, where they use strong encryption to protect the e-mails when they’re in transit … but for their own business purposes they have to be able to access the underlying content and they do that for a variety of reasons. One is potentially to serve you advertisements, [or] for data security – they can scan malware, so they can scan for spam, and things of that nature.
“And so when we look out and see that there are companies now that have figured out how to do that balance – how to ensure strong protections and security for their data but also have access to it – it’s difficult when we hear [from security experts] that it’s technically impossible to do this,” Mr. Raj continued.
This may be a superficially attractive argument for some. But it completely misses the point of what security experts are actually arguing. Even more importantly, it utterly undermines Comey’s fearful vision of universal encryption-driven anarchy.
The fact is, Comey and his colleagues are absolutely right: There are a wide variety of very popular services that do not deploy end-to-end encryption as feature, so they can offer other features for which there is enormous consumer demand. Such features include the ability to easily store and search all of your messages from multiple devices, or to have the service provider sort for spam or viruses, or to use services for free by letting the companies make their money from targeted ads based on your message content.
In other words, there is serious market demand for – and thus much money to be made, and much incentive for companies to offer – features that rely on data not being end-to-end encrypted, data that can then be handed over to government agents with a search warrant.
That simple technical and economic fact is not going to change, which means there will always be huge data troves – e-mail accounts, social media accounts, data backups, photo archives – that the government can still obtain.
Therefore the “universal encryption” narrative isn’t a realistic prediction at all; it’s just a dystopian fantasia meant to scare politicians and voters. Nor is the government “going dark”; rather, it’s enjoying a Golden Age for surveillance, and that Golden Age isn’t ending any time soon – even if there will also always be some companies offering end-to-end encrypted services to those who value security as a feature more than those other features.
And that’s the key: People will always want and need to treat different communications differently, using different types of services with different types of features. Just as in the real world, where we keep some letters in a permanent file while other things we would only say in a whisper that’s never to be heard again, so, too, in the online world do we use Twitter for one kind of communication, Gmail for another, and Whatsapp for another, balancing features like accessibility and security and searchability and cost accordingly.
No one is saying that Gmail is “fatally insecure,” but unencrypted messages stored on an e-mail server will always be more vulnerable to a Sony-style hack or a nosy boyfriend who’s stolen your password than communications that are ephemeral and end-to-end encrypted.
Many (but not all) people, for many (but not all) messages, are willing to make that trade-off based on the expectation that the security of Internet giants like Google and Microsoft will hold off all but the most well-resourced, state-sponsored attackers. (Notably, both companies’ computers were successfully penetrated a few years ago by Chinese intelligence, who ironically went straight for their lawful intercept systems in order to find out who the US government was spying on.)
But in the end, it’s our choice – our decision.
FBI Director Comey, however, wants to put his hands on the scale and decide that trade-off for us – for every American and for every communication. In the process, he wants to push the entire Internet in a direction that would be bad for cybersecurity, bad for innovation, bad for our digital economy and bad for global competitiveness. Bad for you. Bad for me. Bad for the Internet.
We shouldn’t let him.
Kevin Bankston is the director of New America's Open Technology Institute, a nonprofit technology policy center dedicated to fostering stronger and more open communities by building a stronger and more open Internet. Follow him on Twitter @kevinbankston.