2016: The year where identity is everything in cybersecurity
Loading...
Do you remember 2013? That was “the year of the mega breach,” thanks in large part to the world getting to know one Edward Snowden.
For really the first time, the broad general public came up close and personal with the impacts of a data breach.
While that trend of megascale data breaches continued in 2014, last year saw a slightly different turn: digital attackers targeted more personal, longer lived information than the credit card caches and troves of government documents that had been unearthed before.
Hackers cracked the Office of Personnel Management’s database, took health records from major American insurance companies, and downloaded intimate data from adults (Ashley Madison) and children (Hello Kitty) alike.
You could say 2015 was the year that data breaches got personal.
The moral of that story? No company or agency is safe from attacks; corporations that we trust with our information, our family’s information and even our kids’ information was, is, or will be targeted. We need to accept that the world has changed.
In 2016, we hope, we’ll solve the problem before we get taught a lesson.
This is the year that we learn digital identity is everything. But why is that?
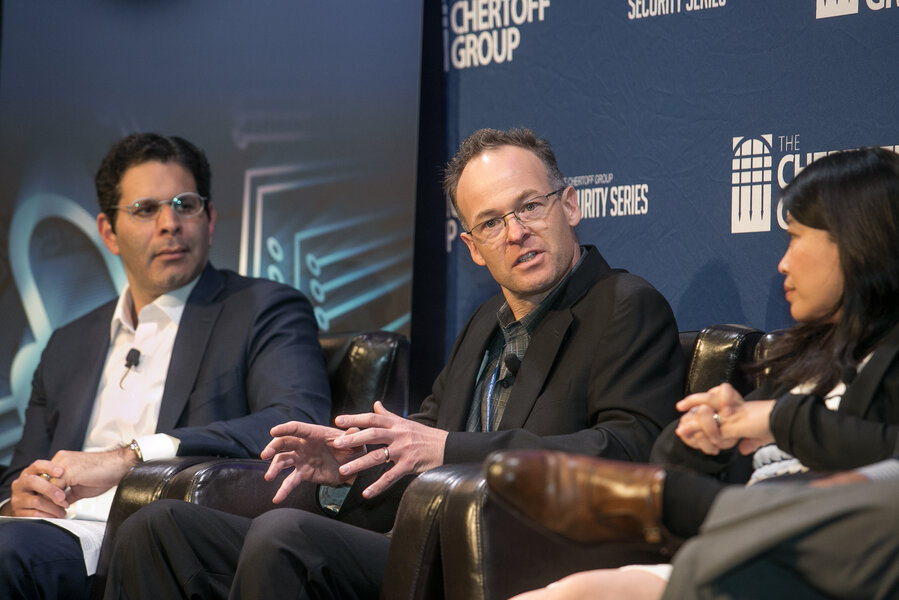
The ability to determine someone’s digital identity is proving an enormous economic driver, as industry experts discussed at a recent Chertoff Group event in Palo Alto, California.
Consider how morning driving commutes will be changed when the billboards can read your car’s IP address and serve advertisements knowing the identity of the person at the wheel, as Chenxi Wang, a vice president of strategy at startup Twistlock put it at the event.
Now consider that more than two thirds of MGM Resorts International revenue now comes from non-gaming elements of the customer experience in its bevy of US and international properties, said Scott Howitt, chief information security officer (CISO) and senior vice president of MGM at the Chertoff Group event.
“It’s become an every-day conversation for me and central to everything I do.”
Mr. Howitt said.
But as with everything in digital security, these new economic opportunities bring new risks.
Companies have multiple users entering their systems and accessing their data: employees, contractors, vendors, suppliers, partners, and even customers. Considering the sheer volume of users, applications and various levels of data access, it is easy to imagine an enterprise managing over a billion points of access.
But these points of access can easily become a billion points of exposure, too. Behind all those points of access is a person – an identity.
Securing the identities of those moving in and out of our increasingly complex and economically vital systems means everything.
And that means, in 2016, identity is everything. Identities in an organization are who “hold the keys to the kingdom” and therefore will be targeted. In 2016 more than ever, securing those identities should be at the core of every enterprises' security program.
As the world evolves, so must our digital security. It used to be that network security was all we needed since intruders had to either come into the physical location or hack from outside the network. Now, hackers have turned to the weakest link in the security infrastructure: us. People. Users. Identities.
It has become clear that the notion of network-centric security is a strategy of the past. A paradigm shift happened in 2015 where a user-centric approach of security emerged as the most robust strategy to secure an organization’s assets in our distributed information technology world. Only then can we have a common understanding of who should have access, who does have access, and how they are using their access.
“It’s now become very clear that we’ve done what we can at the perimeter, we’ve done what we can on individual systems, we’re doing what we can on monitoring, we just have to get to the heart of the matter,” said Joe Gottlieb, senior vice president of corporate development at SailPoint on a panel at the Chertoff Group event. “Security is behind. Business wants to go faster. Our growth and our opportunity is helping companies be more thorough about this.”
SailPoint delivers solutions for compliance, provisioning, access management, and identity analytics. Follow SailPoint on Twitter @SailPoint.