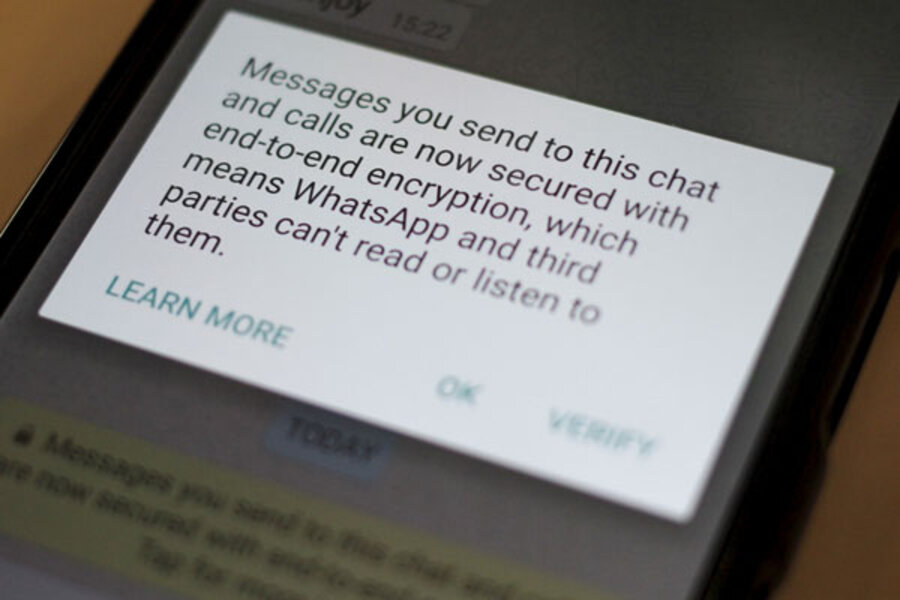
Yes, your encrypted WhatsApp messages are still secret
Loading...
If you’ve recently seen headlines or tweets claiming that hackers can get around WhatsApp’s encryption, don’t believe the hype.
Last week, the London cybersecurity firm Positive Technologies boasted that it had discovered a vulnerability in a fundamental part of the mobile communications infrastructure that rendered WhatsApp encryption useless.
Later, however, the company admitted it may have overstated the scope of the problem. Yes, they say criminals may be able to take over your WhatsApp or Telegram account by exploiting flaws in the Signaling System No. 7 (SS7) network that routes calls and text messages around the world.
"It wouldn’t render the encryption ineffective, but it would still expose the user to be impersonated, and continue to be impersonated," said Alex Mathews, a spokesman for Positive Technologies. "The whole reason to come out with this angle is to change the way the they are working," referring to WhatsApp and Telegram security settings that he claims don't put enough of an onus on users to verify their identity.
But experts don’t think that just any hacker can break into your WhatsApp account. They’d need access to SS7 – typically controlled by phone carriers and national operators – specialized software, the user’s cellphone number, and the subscriber identity.
What can be exploited, according to Mr. Mathews’ team, are security protocols in SS7 that could allow hackers to steal verification codes to register fraudulent accounts. In fact, using a Linux-enabled laptop loaded with SS7 access and specialized software, Positive Technologies said it could impersonate WhatsApp and Telegram users.
The Positive Technologies report followed a widely publicized segment on SS7 vulnerabilities on "60 Minutes," adding to the hype about flaws in the mobile backbone. On an April episode of the CBS News program, German security researcher Karsten Nohl exploited SS7 – which transfers mobile traffic from cellphone towers to the Internet – to snoop on an iPhone belonging to Rep. Ted Lieu (D) of California, reading calls, e-mails, and text messages.
"This can be done either by a telecom operator or by third-parties that manage to co-opt or infiltrate a telecom provider," said Markus Ra, a Telegram spokesman. WhatsApp representatives declined to comment on the research.
Encryption experts agree that the attack found by Positive Technologies could be challenging to pull off.
"I think for the moment, we should not get caught up in the hype," said Matthew Green, an assistant computer science professor at Johns Hopkins University. For a hacker to the mobile backbone, “you either have to find some business that’s really shady or that’s not doing their homework."
Since most SS7 networks are closed systems and not connected to the open Internet, it has generally proven difficult to get inside the network without proper permits and sophisticated telecommunications equipment.
But as more businesses are reselling access to the mobile backbone, the US government wants users to stay alert to the threat. After appearing on "60 Minutes," Mr. Lieu called on the House Oversight Committee to investigate flaws in SS7. The Federal Communications Commission also plans to look at a strategy to transition away from the network.
In the meantime, security savvy users have a few options to protect themselves against SS7 attacks. WhatsApp allows users to enable notifications that show changes in contacts’ security information, though it’s not a default setting. Telegram offers two-step verification for accounts, but that’s not a default either.
The cryptographer that designed WhatsApp’s encryption protocol says the attacks would do little to stop the service’s users from communicating in private.
“Man-in-the-middle attacks are possible, and always will be," said Moxie Marlinspike, the cryptographer who designed the Signal protocol used to encrypt WhatsApp messages, referring to a type of cyberattack that’s been used by hackers and intelligence agencies to intercept communications and spy on Internet users. "This is exactly what end-to-end encryption was built to protect against."