Iran-Saudi Arabia row adds fuel for hackers on both sides
Loading...
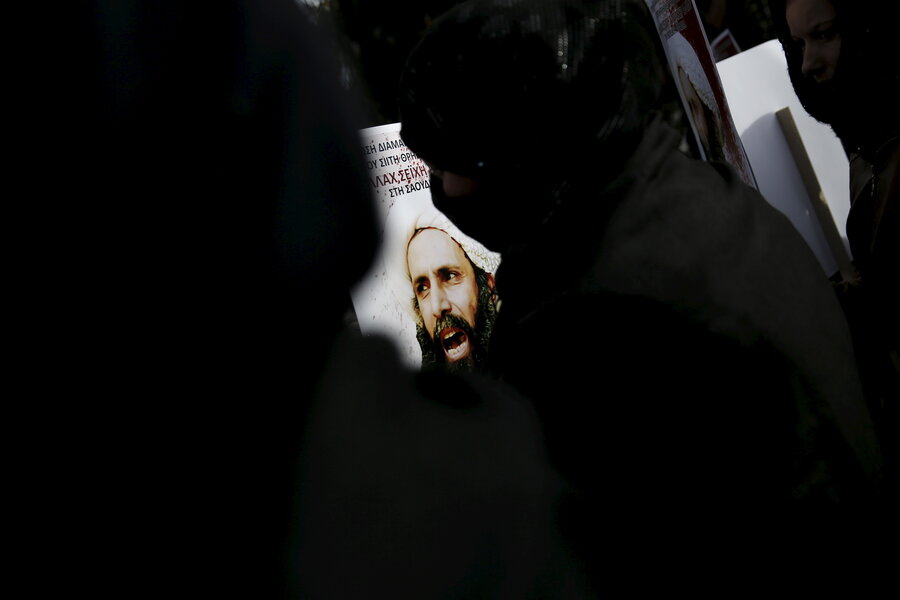
Longstanding tension between Iran and Saudi Arabia boiled over earlier this month after Saudi authorities executed a leading Shiite Muslim cleric. Now, the turmoil that followed the death of Sheikh Nimr Baqir al-Nimr appears to be moving online.
In the wake of Sunni Saudi Arabia and Shiite Iran severing diplomatic ties, unknown hackers attacked key websites belonging to the Saudi Defense Ministry in a digital assault that experts worry could set off a broader sectarian-fueled cyberconflict in the Middle East.
"Severing diplomatic relations between [Iran and Saudi Arabia] will not only escalate the cyberwar, but will escalate it fast," says Abdullah Al Ali, chief executive of Cyberkov, a Kuwait cybersecurity firm.
While no group has claimed credit for the Saudi cyberattack (Iran’s Fars News Agency linked it with Saudis protesting al-Nimr’s execution), the attack comes as Iran appears to be expanding its offensive capabilities in cyberspace.
In December, US officials said that the Iran Revolutionary Guard Corps hacked into e-mail and social media accounts belonging to Obama administration officials. Also, in the same month, The Wall Street Journal reported that the Department of Homeland Security had connected Iran with a 2013 hack against a small dam outside Rye, N.Y.
If the flare-up between the rival countries that have long jockeyed for power and influence in the Middle East spills onto the Internet, it wouldn't be the first time that Iran and Saudi Arabia – or the two nations' many surrogates – have battled in cyberspace.
In 2012, US officials claimed that Iran developed the Shamoon virus that wiped out the computers of Saudi Arabia’s top oil company, Aramco. Last year, in the wake of Riyadh’s bombing campaign in Yemen, a group calling itself the Yemen Cyber Army claimed responsibility for breaching the Saudi Ministry of Foreign Affairs, allegedly stealing the details of thousands of top officials and passing that information to Wikileaks. Iranian officials have said that their government has provided weapons and funding to Shiite Houthi rebels that pushed out Yemen's civilian government last year, which was backed by Saudi Arabia – prompting Riyadh to begin airstrikes in the country.
"Judging from the examples of Aramco and the foreign ministry, we believe Iran follows a methodology of deep infiltration and long term data extraction,” says Cyberkov’s Al Ali. "[Iran is] silently waiting inside compromised networks, and then when the time is right from a political point of view the attack is made visible to the world either by destruction of data or disclosure of information to leak information or embarrass Iran's adversary."
Recorded Future, a Somerville, Mass., cyberthreat intelligence firm said details discovered in the Ministry of Foreign Affairs attack were similar to the Aramco hack, suggesting that Iran had a hand in aiding the Yemen Cyber Army.
The firm's report on Iranian capabilities, conducted last year using open source intelligence, found that Iran had more than 6 million more Internet users than Saudi Arabia, and that Saudi hackers were mainly focused on domestic campaigns, such as Anonymous’s #OpSaudi, an ongoing protest of the monarchy. Anonymous also knocked several Saudi government websites offline in September to protest the death sentence against Ali Mohammad Baqir al-Namir, arrested for his role in pro-Arab Spring protests in 2012.
During the Yemen campaign, Saudi and Iranian hackers seized social media accounts and vandalized websites – culminating in pro-Saudi attacks against the Fars News Agency. Recorded Future found that Iran has mounted far more digital attacks than Saudi Arabia, even though Riyadh has long standing relationships with US defense contractors that provide cybersecurity services such as Lockheed Martin and Raytheon, which upgraded the kingdom's Patriot Missile Defense System. The Russian Internet security provider Kaspersky Lab has also bolstered its presence in Saudi Arabia.
"You can go buy ten fighter jets, a hundred fighter jets, or fortified tanks – the Saudis know how to do that," said Christopher Ahlberg, chief executive officer of Recorded Future. "But it's a different sort of thing to buy or institute a cyber capability that Iran has very cautiously built over time, starting in their universities, even younger."
Many experts say that Iran began focusing on building up technical talent and cyberwar capabilities following the discovery of Stuxnet, the computer worm that attacked the Islamic Republic's nuclear program.
"Over that time we’ve been able to see their capabilities increase in terms of tactics, techniques, and procedures," said Jon Miller, vice president of strategy at Cylance, a San Diego cybersecurity company.
While the country started with more basic attacks such as denial-of-service attacks and website defacements, their capabilities have advanced rapidly, said Benjamin Runkle, a former Defense Department and National Security Council official who currently writes about cybersecurity challenges in the Middle East. "Their development has been similar to China. They’ve moved on to more sophisticated capabilities."
Mr. Runkle pointed out in a recent piece for Passcode that Iranian cyberattacks have increased so much that the State Department issued a report in May cautioning US businesses with overseas operations to be more vigilant. "It shouldn't come as any surprise that Iran is constantly sharpening its arsenal of digital weapons," he wrote, "cyberspace is increasingly critical front for most modern nation-states."