Net neutrality could hinder efforts to safeguard Web, worry security experts
Loading...
Some security experts worry Thursday’s net neutrality ruling could limit broadband providers when it comes to rooting out malicious Internet traffic.
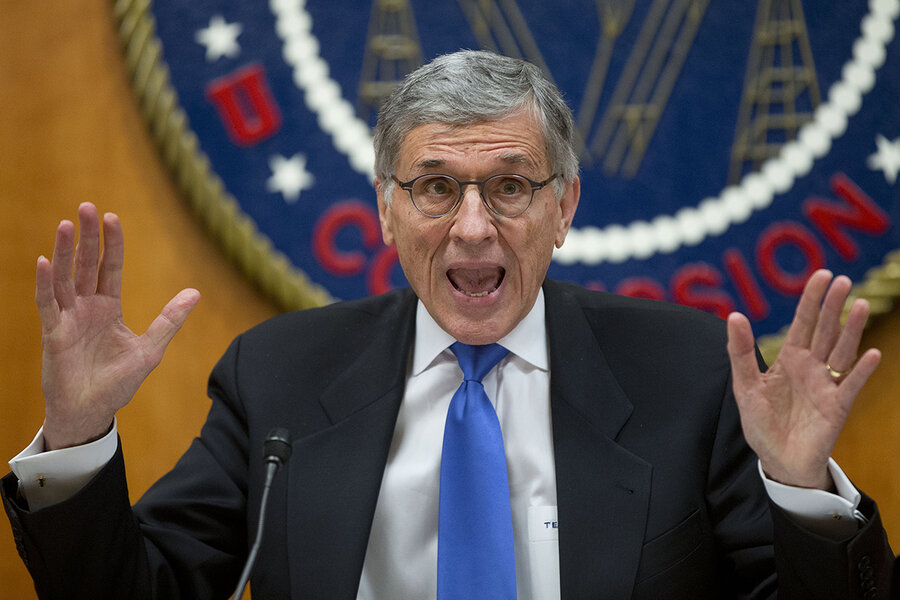
In a decision welcomed by consumer advocates, tech companies, and digital rights groups, the Federal Communications Commission voted by a 3-2 margin to begin classifying broadband as a utility.
In essence, the ruling classifies Internet service providers, or ISPs, as public utilities such as phone companies. It prohibits providers from creating Internet "fast lanes" to deliver any Web content faster for a fee – or slowing down traffic based on content.
But problems may arise if ISPs start equating net neutrality with “common carrier” status, says John Pescatore, director of emerging security threats at the SANS Institute in Bethesda, Md.
Phone companies still operate under common carrier status and are prohibited form treating calls differently based on where they come from, who is calling, or what might be said on the call. As common carriers, phone companies are prohibited from looking into the content of what they transport.
The downside is that phone companies do nothing to filter out bad or annoying calls. It took a separate law to get them to allow a Do Not Call List, Mr. Pescatore says.
“Net neutrality has not been defined the same way,” he says. “But it is likely the ISPs will treat it that way and make absolutely no progress toward filtering out bad stuff before it reaches the end user,” he says.
Unless the FCC specifically dictates that ISPs must take specific measures to control bad traffic, net neutrality could slow down some of the progress providers have made ensuring a safer Internet, says Pescatore.
While net neutrality supporters view Thursday's ruling as vital to ensuring a free and open Internet, much depends on how the rules are interpreted, says John Bambenek, founder of Bambenek Consulting, a cybersecurity firm in Champaign, Ill.
For instance, he says, there is a potential the rules could create gray areas with regard to the use of certain traffic inspection tools used by providers to filter out malicious traffic and spam. Anything that would impose a ban on traffic throttling without accommodating provisions for handling spam or botnet traffic could create a problem for users, Mr. Bambenek says.
The reality is that not every bit of traffic that flows on the Internet is equal, he says. For instance, a lot of content that is malicious or spam can often consume a disproportionate amount of network resources. An indiscriminate ban on traffic throttling without clear language accommodating these issues could result in a less secure Internet, he said.
“My concern is that the FCC doesn’t understand these technical nuances well enough to avoid collateral damage," says Bambanek. “There is a lack of real understanding of how this thing works.”
Those types of concerns about net neutrality aren't new, and many of its most ardent supporters have tended to dismiss the security concerns associated with open internet provisions.
“While ISPs could use [net neutrality rules] as an excuse to become lax when it comes to security, they were under no obligation to do anything regarding security before they were reclassified, either,” says Jeremy Gillula, staff technologist at the Electronic Frontier Foundation. “They could use it as an excuse, but it would be just that, an excuse."
In addition, the general understanding is that the new rules do provide for reasonable network management, including for security. Gillula says there’s little reason to believe that broadband companies will be forbidden from making their networks secure.
“With that said," says Gillula, "I'm not sure many people would want ISPs looking at the contents of their packets in the name of filtering out bad stuff.”