iCloud hack shows the serious problem with living la vida Apple
Loading...
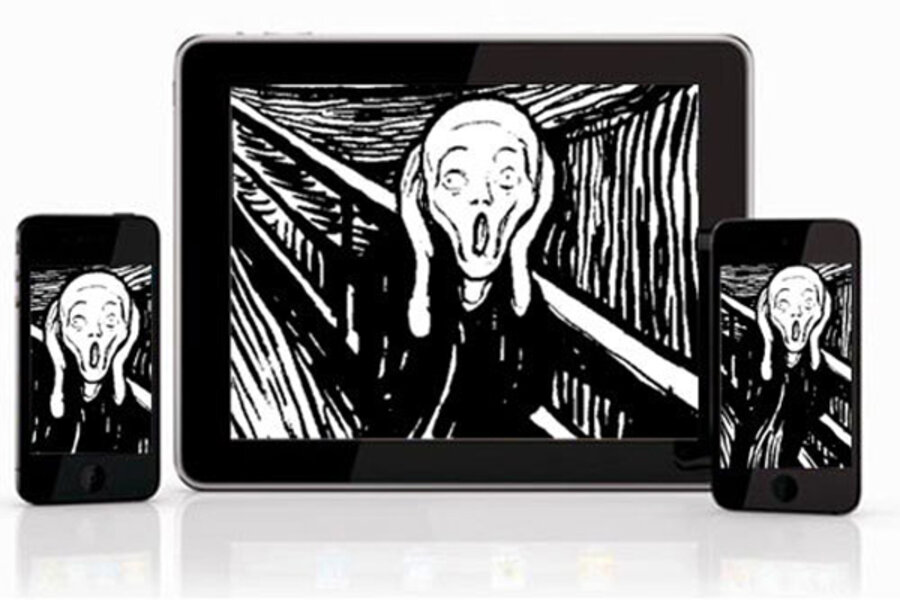
Imagine you're playing with your young daughter when suddenly your iPhone goes blank. You check your iPad, but it's been wiped clean too.
You run to your laptop, and catch it erasing all its own data. You get online, but both of your email addresses have been hijacked, your online storage has been emptied, and someone else is using your Twitter account.
This nightmare scenario happened in real life Friday afternoon for Mat Honan, a technology journalist based in San Francisco.
Someone took over Honan's Apple account, which let him remotely wipe Honan's iPhone, iPad, and MacBook, then leverage that power to take over Honan's Google and Twitter accounts as well, plus the Twitter account of Gizmodo, the tech blog Honan sometimes writes for.
Yet Honan's enemy wasn't an elite hacker who used advanced techniques to crack Honan's password. Instead, the attacker simply placed a call to Apple tech support and convinced Apple to give him control of Honan's Apple account.
Tale of the tape
"At 4:50 PM, someone got into my iCloud account, reset the password and sent the confirmation message about the reset to the trash," Honan wrote on his Tumblr account, which was spared. "At 4:52 PM, they sent a Gmail password recovery email to the .mac account. Two minutes later, an email arrived notifying me that my Google Account password had changed.
"At 5:00 PM, they remote wiped my iPhone. At 5:01 PM, they remote wiped my iPad. At 5:05, they remote wiped my MacBook Air. A few minutes after that, they took over my Twitter." (Honan posted a screen grab of the notifications his Gmail account received.)
The attacker, identifying himself as part of a hacker group calling itself "Clan Vv3," used Honan's Twitter account, "@mat," to post, "@gizmodo Tell this dumbass employee mat he's an idiot for using insecure email services, having a 3-letter Twitter, and having access to [Gizmodo]."
Then he or she took over Gizmodo's Twitter account and posted offensive messages for about 15 minutes.
Clan Vv3 has been hijacking the Twitter accounts of minor celebrities for several months, for example one belonging to comedian and TV star Whitney Cummings in June.
After a distressing couple of days, Honan has now regained control of his Twitter and Google accounts and has an appointment with an Apple Store Genius Bar [on Aug. 6] to try to recover the data on his Macbook.
Technology is smart, but people are dumb
The entire episode should serve as a warning to others about two issues.
First, Honan was overly reliant on one company's services — in this case, Apple's. Honan backed up his MacBook, his iPhone and his iPad, but he did so only to iCloud, Apple's own cloud-storage service. All of that was destroyed with one password.
Cloud storage is great, as long as you have reliable Internet access, but it's best to have backups you physically control — for example, on an external hard drive.
Honan's ".mac" email address was the emergency confirmation address that Honan had instructed Google to notify if anything went wrong with his Google account.
So when the attacker, posing as Honan, pretended he'd forgotten his Google password, the confirmation email went to the .mac address, which the attacker already controlled.
Once the attacker had control of the Google account and the Gmail service, he used that to take over Honan's Twitter feed.
Honan could have used Google's two-factor authentication service, which upon a password-reset attempt sends a text message to a designated cellphone as well as an email to a non-Google email address for confirmation. But that wouldn't have prevented the wholesale wiping of all his Apple products.
Second, no matter how good security technology gets, it will never be able to stop "social engineering" attacks, or what your grandparents would have called a good con job.
In the early '90s, famed hacker Kevin Mitnick found that the best way to get into any secure system was to simply telephone the system's administrators and convince them you were an employee who'd forgotten his password.
Twenty years and thousands of successful hacks later, the same method still works on the world's most valuable and most high-profile technology company.
It's not clear exactly what the attacker said to the tech-support person who answered the phone, but as some experts have pointed out, Apple should not give frontline tech-support staffers the ability to reset user passwords.
Most online-account hijacks are the result of weak passwords — the passwords are too short, too obvious, used in too many places or limited to lower-case letters.
Honan's password was rather short, but it was unique and used mixed characters. "My password was a 7-digit alphanumeric that I didn’t use elsewhere," he wrote on his Tumblr page.
But it didn't matter. As Sascha Segan of PC Magazine tweeted, "The strongest password in the world wouldn't have saved @mat."