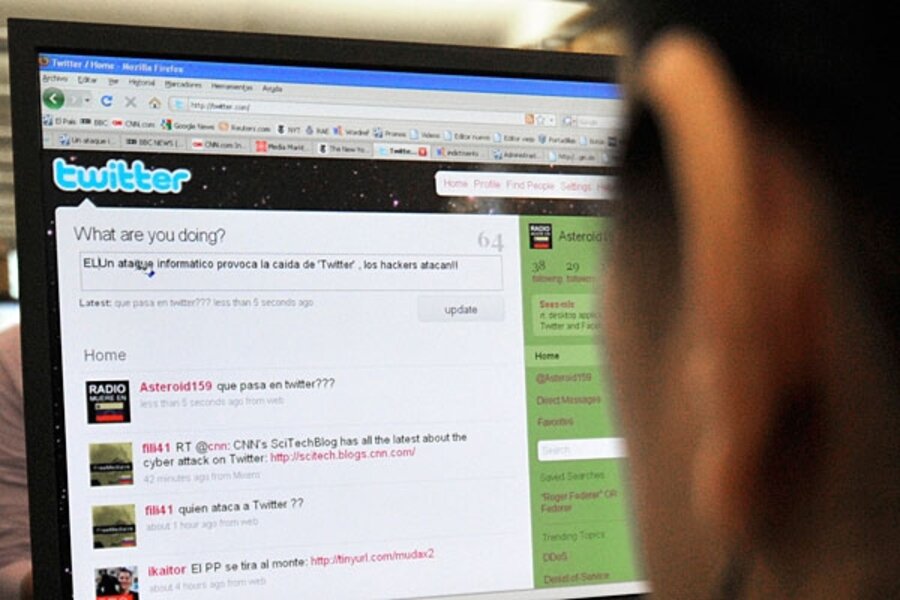
Twitter crash points to rise of denial-of-service attacks
Loading...
| San Francisco
Denial-of-service hacker attacks such as the one that took down microblogging site, Twitter, on Thursday morning are proliferating on the Internet, and getting increasingly organized.
“Attacks such as this are malicious efforts orchestrated to disrupt and make unavailable services such as online banks, credit card payment gateways, and in this case, Twitter, for intended customers or users,” said Twitter cofounder Biz Stone in a blog post Thursday morning.
Thursday morning saw something of a social media meltdown with Facebook saying that it was experiencing problems, too, due to a similar hacker strike. The blogging Web site LiveJournal also confirmed that it was the victim of a denial-of-service hit. Earlier this week, hackers also temporarily shuttered the popular online gossip site Gawker.
Disruptive Denial-of-service (DDoS) attacks cripple Web sites by flooding it – usually through a “botnet,” or network of computers strung together for malicious purposes – with bogus service requests.
“This denial of service [problem] is one of the most difficult classes of attacks to defend against,” says Hugh Thompson, program committee chair of RSA Conferences, the leading conference for information technology security professionals.
Synchronized attacks?
“Over the last five years, this has gotten a lot more organized,” he says. If a barrage of bogus requests come from one server, the attacks can usually be defended. But because botnets have grown so large – connecting so many different computers – it's becoming a big challenge.
“These attacks are the big hammer of attacks because everyone is potentially vulnerable to it,” says Mr. Thompson.
While Thursday’s attacks on Twitter and LiveJournal may amount to minor inconveniences, experts say that the increasing power of these attacks could boot entire companies off the Internet.
“There are hundreds of DDoS attacks that occur on a daily basis... Many of these attacks are small and they are not necessarily against a high-profile organizations. Not every botnet wrangler is out to get Microsoft,” says Howard Eland, senior director of content propagation and resolution for Afilias, an Internet infrastructure provider. These underground networks can target companies for extortion, he adds, or just to make them look bad.
So who is controlling these malicious botnets? As they become more complex and larger, the origins of the hackers are increasingly cloaked.
“It’s hard to pin down a single command and control structure,” says Mr. Eland.
Targeting Twitter
These sorts of attacks are hitting more popular sites and news sites to send a message — often a political message.
“A number of these [attacks] are political messages, especially if you look at the attacks on US government sites," says Paul Judge, chief technology officer of Purewire, a Web security service.
So why was Twitter attacked? Probably because it has grown so big – and increasingly seen as an important vehicle for free speech around the world – that it's become a tantalizing target for hackers.
“If you think about Twitter – in some ways and in some countries – it has almost turned into critical infrastructure,” says security expert Thompson. “If you think about it from that perspective, it’s a victim of success. There are more and more reasons to want to take it down.”