Opinion: Why Washington needs more hackers
Loading...
A dark room. A hooded figure hunched over a keyboard. Lines of code on a monitor barely illuminate his face. An expression of glee as thousands of dollars are siphoned out of a victim’s bank account, followed by a pained look as a voice calls out, “Son, come take out the trash.”
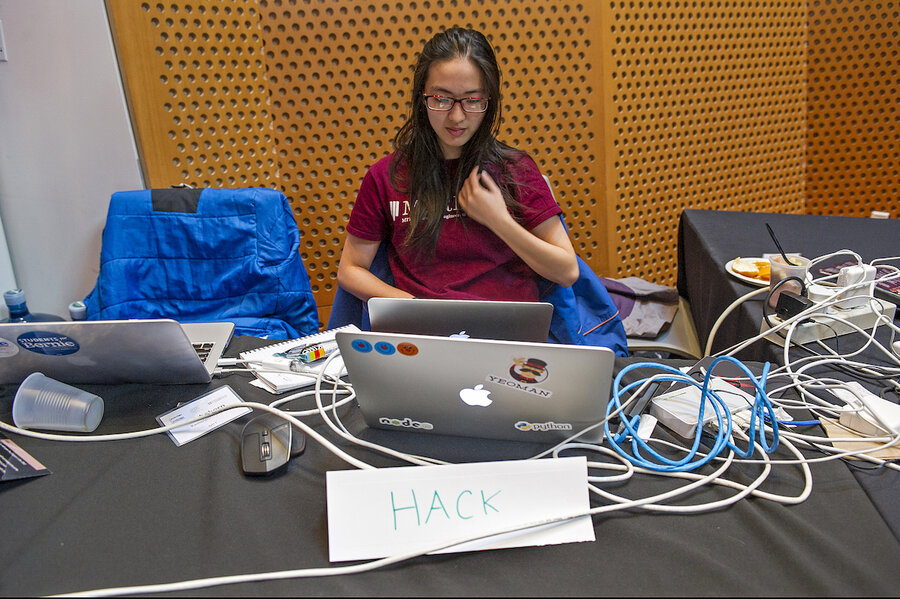
The stereotypical image of the teenage hacker in his parents’ basement is everywhere, even in our presidential debates. And yet, it couldn’t be further from reality. Hackers are a diverse bunch: young and old, PhDs and high school dropouts, and, increasingly, women.
But the one thing that unites all of the hackers I have met is intense curiosity. They want to know how things work, and they find out by taking things apart. Unfortunately, this proclivity has led to a number of misconceptions about hackers. Americans celebrate creators, inventors, and entrepreneurs, so the act of deconstructing others’ works is often seen as malicious.
This attitude, while pervasive, is misplaced. There are bad actors out there, who aim to use their skills to steal, extort or corrupt. But the majority of hackers, or cybersecurity researchers as they are sometimes known, are interested in solving the puzzle of how something works, probing its flaws, and then helping to shore up the weaknesses. This last point is very important: not only are most researchers uninterested in nefariously exploiting the vulnerabilities they find, they actively want to help fix them.
That help is sorely needed. Every day, thousands of new software products come on the market, from apps to connected devices. A car, for example, can have over 100 million lines of code powering its systems. These immensely complex systems inevitably contain errors. While most errors are innocuous – a garbled webpage or a crashed app – some can pose major security risks if not patched. The breaches that fill the headlines, from the Democratic National Committee to the Ukrainian power grid, are often a result of these vulnerabilities.
Knowing these risks, companies are increasingly turning to hackers for help. Rather than threatening security researchers with legal action for disclosing code errors, forward-thinking businesses are providing clear avenues for hackers to report their findings.
These vulnerability handling processes respect the time and effort hackers put in to discovering bugs by keeping clear lines of communication open and, often, providing some sort of acknowledgement to the finder. Occasionally, that acknowledgement comes in the form of cash, a “bug bounty” based on the severity of the issue. Vulnerability disclosure policies leverage the power of the crowd to improve security and save companies money.
While vulnerability handling has exploded across industry in the past several years, the federal government has lagged behind. Despite operating tens of thousands of websites and myriad other software products, the government has not provided any clear avenue for patriotic-minded hackers to disclose security issues.
Thankfully, forward-thinking leaders in the government are beginning to change that. Last year, the Department of Defense hosted the first-ever federal bug bounty program, “Hack the Pentagon.” Over four weeks, 1,400 hackers discovered more than 125 security vulnerabilities at a fraction of the cost per bug of existing programs. The Pentagon has since begun an expansion of the program, and the Internal Revenue Service announced that it, too, would begin offering bug bounties on a limited basis.
More importantly, federal agencies are finally beginning to welcome public service-minded hackers with full-fledged vulnerability disclosure policies. The General Services Administration released a draft policy for comment in October, and, in November, Secretary of Defense Ash Carter unveiled a Pentagon-wide policy. I commend outgoing Secretary Carter and the other leaders in these agencies for their efforts to treat hackers not solely as adversaries but as valuable allies as well.
These policies are nascent and will inevitably need some tweaking. They also cover only a fraction of the services provided by the government. But they represent an inflection point in our thinking about the security research community, and I hope the new federal Chief Information Security Officer makes expanding these programs a priority.
Changing the image of hackers is tough. But I am glad the federal government is finally moving beyond stereotypes and embracing the potential for security researchers to improve our nation’s cybersecurity.
Congressman Jim Langevin (D) of Rhode Island is the cofounder and cochair of the Congressional Cybersecurity Caucus, and a senior member of the House Armed Services and Homeland Security Committees.