High-stakes DARPA hacking contest pits computer against computer
Loading...
Jim Alves-Foss probably isn't the only competitor dealing with pregame jitters ahead of the Pentagon's inaugural machine versus machine hacking contest in Las Vegas on Thursday.
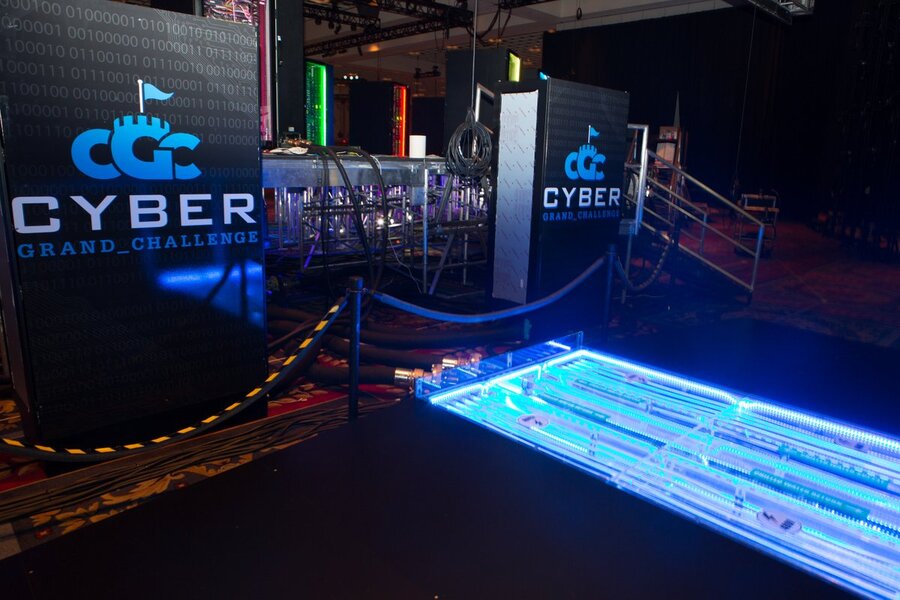
As part of one of seven teams that will vie for supremacy in the high-stakes Defense Advanced Research Projects Agency (DARPA) Cyber Grand Challenge, his team's supercomputer will attempt to look for software flaws and defend digital networks in front of a live audience – along with blow-by-blow commentary from announcers – in something of a virtual gladiator battle royale.
But Mr. Alves-Foss' machine is hardly combat tested. The computer science professor at the University of Idaho is used to running his machines inside labs at the Center for Secure and Dependable Systems (CSDS) – not in front of cheering techies. And the anxiety of preparing for the contest, which DARPA designed to spur more innovation in cybersecurity automation, almost knocked him out of running ahead of Thursday's digital kickoff.
Just before his team submitted the software flaws they had found in the final qualifying round of DARPA's challenge, he made a near fatal error. "I deleted half the work our machines had done in the past 23 hours," he said. "I was so mad at myself."
But for his team to win Thursday's $2 million purse, the CSDS team will need to operate flawlessly. In the DARPA Cyber Grand Challenge, engineers and researchers aren't allowed to intervene. Thursday's contest is meant to see how computers can perform on their own. One simple glitch or piece of bad code could spell the end for any one of the seven teams.
"Cyber Grand Challenge is an attempt to tie all of [the research] into a system that does everything and makes all of the decisions," says Mike Walker, DARPA’s program manager for the competition. "It's a huge jump for the field that we’re asking them to make."
DARPA has been working on its challenge for the past three years and held a series of preliminary contests to whittle down the competition to the best teams, which are comprised of experts at defense contractors such as Raytheon and researchers at prestigious university computer labs such as Carnegie Mellon University and the University of California, Berkeley.
DARPA hopes that computers will eventually find bugs – and fix them – much faster than humans. Currently, software flaws similar to those that Grand Challenge competitors will attempt to find and patch often go unnoticed in the real world for many months, says DARPA's Mr. Walker, giving attackers the chance to steal financial data, valuable personal information, or health records. And even when a patch is discovered, it can take days for security professionals to fix the flaws.
"We want to build autonomous systems that can arrive at their own insights, do their own analysis, make their own decisions of when to patch and how to manage that process," Walker said in a conference call with reporters last week.
If that sounds ambitious, that's because it is. DARPA has a history of shooting for the moon. The US government launched the agency in height of the Cold War to ensure that US military technology would keep ahead of the Soviet Union and other adversaries. The small department was involved with the earliest version of the internet, an array of advanced weapons systems, nuclear test detection technology, and, more recently, bionic limbs.
To foster the development of smarter computers to autonomously defend themselves, DARPA has invested $55 million on the Cyber Grand Challenge. Some of that money went to the seven teams who were selected to compete in Las Vegas. DARPA awarded each team $750,000 to prepare for Thursday's contest.
As if there wasn't enough for the team to prepare for ahead of the Grand Challenge, DARPA regularly surprised them with pregame challenges and asked teams to implement new pieces of critical software on their computers leading up to the main event.
"In my business, you often have software projects do demos and the last thing you want to do is change the demo the night before, because it’s probably sure to break while you’re doing it," said Jack Davidson, a University of Virginia computer science professor and the co-leader of the TechX team.
A few weeks before the contest, Mr. Davidson said, "I'm a little worried here, because we’re getting to the point where it's time to deliver and we’re still making pretty serious changes."
And that anxiety probably won't subside until one supercomputer is left standing on Thursday. As Davidson said, "Somebody better check my blood pressure before this thing starts."