Experts: Obama’s color-coded rankings oversimplify cybersecurity threats
Loading...
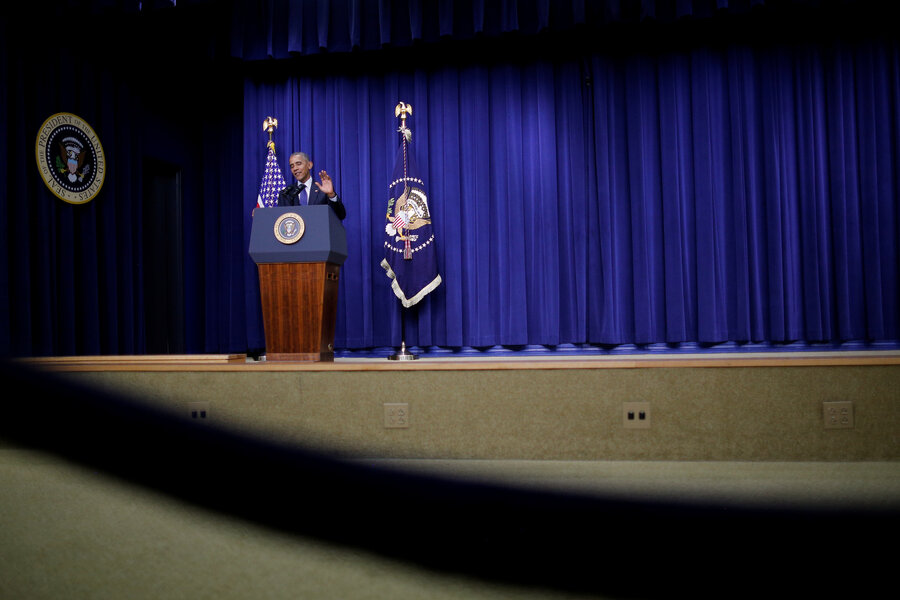
With the Democratic National Committee still reeling from massive data breach, President Obama released a policy directive Tuesday outlining how the government plans to tackle major cyberattacks.
Senior administration officials hailed Obama’s Presidential Policy Directive as a way to provide much-needed clarity about federal agencies’ roles and responsibilities for responding to significant hacks. To help determine whether a breach is significant, the administration released a color-coded system to rank their severity by measuring the potential consequences and the attackers’ suspected intent.
But prominent security experts are panning the directive – particularly the color-coded model similar to the Department of Homeland Security’s abandoned terror alerts – which they say does not properly take into account the complex nature of cyberthreats the country currently faces.
One prominent example is the DNC hack, which cybersecurity experts said wouldn’t clearly fit into any one the administration's categories – even though the accusations that Russian agents were behind the hack raise serious concerns about foreign governments meddling in the US presidential election.
"The problem with these types of documents is that they have a certain type of attack envisioned, the classic, 'Here’s a cyberattack that destroys data or causes physical destruction' and there’s a huge scramble of a response," says Adam Segal, director of the Digital and Cyberspace Policy Program at the Council on Foreign Relations.
"But as the DNC hack shows, or the hack on Sony Pictures shows, there's a lot of hacks that, over time, seem to affect a national or foreign policy interest – and we’re going to have to be more flexible and creative about the way these agencies are going to be involved," Mr. Segal says. "I suspect that the future attacks we face will often not fit into plans."
The release of the presidential directive does not appear to be related to the DNC breach, which resulted in WikiLeaks publishing some 20,000 leaked emails on the eve of the Democratic convention. The document, which has been in the works for several years, is part of a broader Obama administration push to streamline the federal government’s response to cyberthreats.
Still, the close proximity in timing is leaving experts wondering: How would the government respond to something like the DNC hack, based on the new directive? It defines a significant cyberincident as "likely to result in demonstrable harm to the national security interests, foreign relations, or economy of the United States or to the public confidence, civil liberties, or public health and safety of the American people."
There’s little question that taking down the electric grid would have "demonstrable harm" to US interests, says Herb Lin, senior research scholar at the Stanford Center for International Security and Cooperation and research fellow at the Hoover Institution.
"But the public confidence aspect to this – that’s a much squishier thing," he says. "It means you could have small attacks, with small effects, that could have large-scale impact on public confidence. Now the psychology of the American public now becomes a factor."
In the case of the DNC hack, which has already led to the resignation of its chair and is currently fueling party in-fighting at the Democratic convention, for example, Mr. Lin says: "It really scares me that the Russians are starting to interfere in American elections. The idea that we might elect a president in part because Putin favored him is a little bit mind-boggling to me. But I’m just one of 323 million people …. Could it shake public confidence in an election?"
And if the hack does effect an election, it opens the door to even more subjectivity when evaluating economic stability or even national government stability, since, as Lin says, "certainly people have different views about the country’s stability if a certain person is elected."
Lin, who is also on the President’s Commission on Enhancing National Cybersecurity, says he was not briefed about the forthcoming directive or color schema and only saw it with the public release.
Mr. Lin says he would rank the severity of the DNC hack as between orange (high) and red (severe). These are the levels just below the highest, emergency level (black) which signifies there’s an imminent threat to the provision of wide-scale critical infrastructure services or lives of US persons.
Yet, illustrating how people's interpretations of severity rankings could vary widely, Segal says he would lean toward rating closer to a yellow (medium) cyberincident because "we have no idea how the revelations from DNC will play out in the election."
A senior administration official who spoke under condition of anonymity said there are good reasons to have a ranking system when thinking about how to calibrate the government’s response.
"Each level has escalating impacts, escalating aftereffects, escalating rankings of severity to help us gauge the incident, gauge our response and assess the resources we need to bring to bear to respond," the official said. "It’s meant to provide a framework. I don’t think it’s an oversimplification, because it’s a framework – it's going to be something that evolves as we learn more about a particular incident."
Experts also objected to the Obama administration's ranking system of the scope and scale of particular incidents. More severe incidents, the government’s chart implies, include hackers' intent to "cause a physical consequence" or "damage computer and networking hardware." Far lower down on the scale is hackers’ intent to “steal sensitive information” or “commit a financial crime.”
That, adds Lin, "is clearly nonsense."
"I can imagine causing a physical consequence that would be less important than certain financial crimes. I could steal $1 billion from the Federal Reserve, and that is probably more consequential than turning off the generator for the electric power in a town of 20,000 people," Lin says. "Especially if you start taking into account public confidence – if the Fed is vulnerable to that, now I’m really scared."
Experts did praise some elements of the plan, saying the codification of agencies' roles is helpful.
"It’s always a step in the right direction when cyber is prioritized," says Melanie Teplinsky, a former National Security Agency and government official now at American University Washington College of Law. "And so presidential policy directives that focus attention on the need to coordinate what the federal government is doing are certainly to be welcomed."
The directive specifies that if a major hack has even the possibility a nation-state actor is involved, or could have some sort of national security implication, the Justice Department and the FBI will lead the efforts to investigate the crime and hunt down those responsible. The Department of Homeland Security, will lead the government’s efforts to help repair hacked systems and prevent the spread of the threats. The Office of the Director of National Intelligence will help provide intelligence support and related activities.
Another positive step, Ms. Teplinsky says, is the provision that Departments of Homeland Security and Justice will keep an updated fact sheet explaining how private individuals and organizations can contact relevant federal agencies about hacks. That’s something, Teplinsky adds, "the private sector has been clamoring for, for a long time."
However, she adds, "there’s nothing here that’s going to solve the cyber problem. One of the major problems is that when there is a serious cyberincident and the private sector is the target, there aren’t effective responses for the private sector. There needs to be a more effective private sector response in place."