International bust targets BlackShades malware. Is your computer safe now?
Loading...
It’s every computer user’s worst nightmare – a single click of the mouse that unwittingly grants cyber-thieves full access to the user’s files, passwords, even webcams.
Thousands of cyber-criminals gained such access to at least half a million machines in more than 100 countries by tricking users into clicking on a single malicious link that surreptitiously installs a particularly insidious form of malware onto computers, according to federal law enforcement officers.
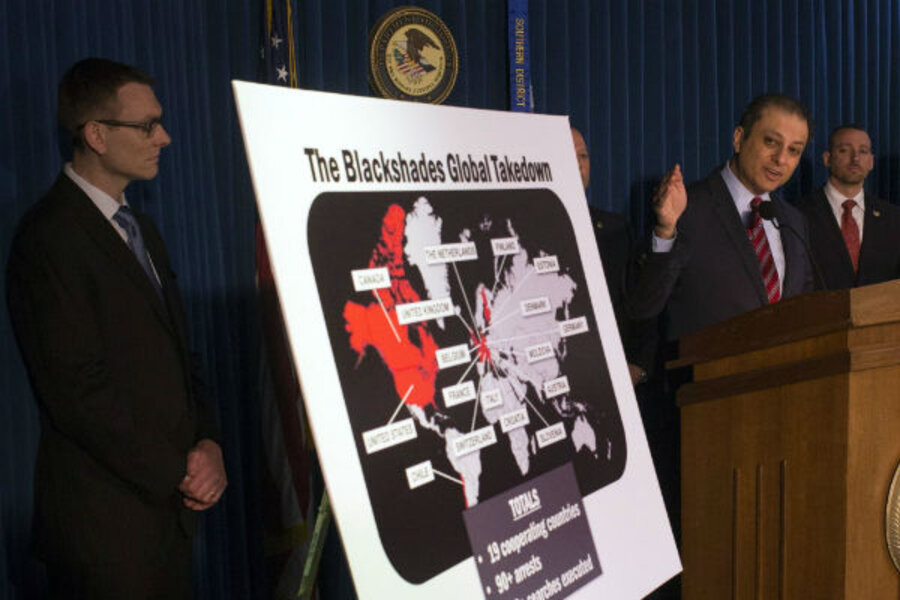
Law enforcement agencies across the globe have launched a concerted strike against developers, distributors, and users of the nefarious BlackShades Remote Access Tool, known as the “RAT,” resulting in 97 arrests in 16 countries, as part of a multinational operation led by the Federal Bureau of Investigation, according to European and US law enforcement officials.
The US Attorney's Office in New York released documents Monday that detail charges against alleged co-creators of the RAT – Swedish national Alex Yücel and American Michael Hogue of Maricopa, Ariz. – as well as three other Americans who bought or helped sell the malware.
The FBI-led operation is part of a broader US effort to crack down on international cyber-crime. Monday’s BlackShades announcement came in tandem with word from Attorney General Eric Holder that the US has filed it first-ever charges for economic cyber-espionage – against five individuals in the Chinese military for allegedly stealing trade secrets from American companies.
The BlackShades documents spell out a set of capabilities that the RAT extends to hackers. Among them are key-logging and form-grabbing features that deliver passwords and other login credentials to hackers, a file hijacker feature that enables hackers to encrypt files and charge victims a ransom to reopen them, and “spreader” tools that use infected computers to post malicious links to a victim’s social media accounts and spread infection via USB devices – all for an average price of $40.
The RAT’s user-friendly interface, accessible price tag, and extensive capabilities have boosted the malware's popularity among hackers, says Kevin Haley, director at Symantec Security response in Culver City, Calif., which assisted in the FBI investigation.
“Somebody with very few skills can simply click on buttons on the screen and they can retrieve anything they want from the victim’s computer,” Mr. Haley says. “They can look through the files. They can take screen shots. They can turn the webcam on. They can even break in and use your instant messaging or your social networks. They really have complete control of your computer. It’s like they are sitting at the keyboard, and they are; they’re just doing it remotely.”
Leo Taddeo, special agent in charge of the Cyber and Special Operations Division for the FBI’s New York office, told reporters Monday that the RAT software “made taking over a computer so easy even a caveman could do it.”
The FBI estimates that the RAT has enabled hackers to penetrate more than half a million computers in 100 countries since 2010.
Haley stresses that a wide range of operators have employed the RAT to meet a diverse set of endgames.
“We’ve seen it used for financial attacks in France, we’ve seen it used against political activists in Libya and Syria. We’ve seen it in multiple countries, Germany, the UK, the Netherlands, France, and on and on,” he said.
The unprecedented global effort sends an important message to would-be hackers, but it has not removed the threat, Haley cautions. Computer users, he says, should be vigilant in maintaining their Internet security systems.
Mr. Yücel faces up to 45 years in prison for his alleged roles as owner and operator of the BlackShades organization and co-creator of the RAT. Brendan Johnston of Thousand Oaks, Calif., is accused of helping to market the malware and of providing technical assistance to hackers who are using the RAT.
Prosecutors have also charged two of BlackShades’ customers with computer hacking.
Kyle Fedorek of Stony Point, N.Y., allegedly bought the RAT in September 2012 and used it to steal financial and other account information from more than 400 victims before his arrest in March.
Marlen Rappa of Middletown, N.J., also faces two counts of computer hacking.
Co-creator Mr. Hogue of Maricopa, Ariz., was arrested in June 2012 and pleaded guilty to two counts of computer hacking in January 2013. He faces a maximum sentence of 20 years, according to the newly released documents. He is currently awaiting sentencing.
Individuals who suspect they may have fallen victim to such an attack can visit www.fbi.gov for information on how to scan their computers for BlackShades files.