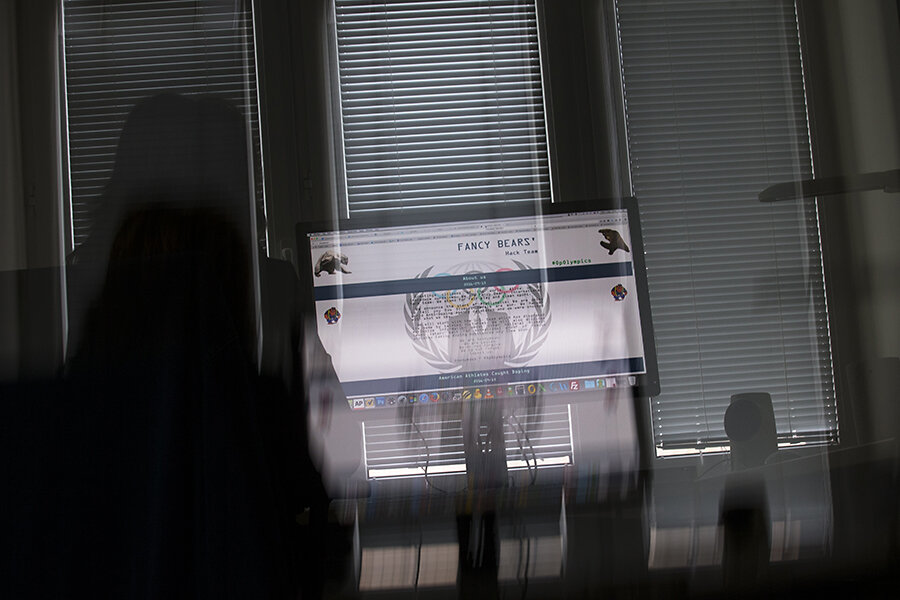
In Russia's cyberscene: Kremlin desires, private hackers, and patriotism
Loading...
| Moscow
While much is known about US cyber-war and -espionage capabilities thanks to the massive data leaks of former NSA contractor Edward Snowden, Russia's capacity for such is much more obscure.
But the experience of Alexander Vyarya, which came to light virtually without notice last year, may offer a few telling glimpses of it.
Mr. Vyarya, a young Russian programmer, was a team member at Qrator, a leading Russian cybersecurity company that specializes in mitigating the effects of distributed denial-of-service [DDoS] attacks. According to his account, given to the independent Russian online news service Medusa, the company was approached by an intermediary from Russia's Ministry of Communications looking for a specialist to help with a particular problem.
Vyarya was "loaned" on an unofficial basis to Rostek, the Russian state technology conglomerate, in early 2015, and sent to an office in Sofia, Bulgaria. There, he was asked to help develop software not to block, but to amplify DDoS attacks. He did – and he was appalled when the program was "tried out" before his eyes on targets like Ukraine's Defense Ministry and the liberal Russian magazine Slon, he later told Medusa. By his account, he told his contact "I am not a hacker," and subsequently fled to Finland.
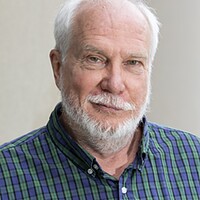
Vyarya's experience – other than the young programmer's attack of conscience and relating his story to the press – is not unusual on Russia's cyberscene, says Andrei Soldatov, one of the country's foremost cybersecurity experts and co-author of The Red Web, a history of the Russian internet – and the security services' efforts to control it – that will be released in Russian next week.
Pinning down specific Russian responsibility for hacking incidents around the world is complicated by Russia's complex arrangement of Kremlin power, semi-official liaisons, and players in Russia's burgeoning IT sector – where the general surge in patriotism since the Ukraine crisis began almost three years ago has made many young specialists more inclined to be quietly cooperative with such requests. What Vyarya describes, Mr. Soldatov says, fits the model.
"Russia's landscape is very complicated, because the private sector is actually far more advanced than the state sector in IT expertise," he says. "Chinese hacking, by contrast, almost totally originates with the security services. But in Russia there is a much wider variety of informal actors."
Cyberwar and cybercrime
According to Soldatov, one of the first examples of politically motivated hacking occurred in the early 2000s, during the second Chechen war, when a group of students in the Siberian city of Tomsk started attacking pro-Chechen websites. Russian security services took notice.
Later, the Kremlin organized several patriotic youth groups, such as Nashi and Molodaya Gvardia, with the aim of using them to crush any "Orange Revolution" type street demonstrations in Russia. Nashi was later implicated in a highly successful DDoS attack against infrastructure in Estonia in 2007.
"It's quite a clever model, since you always have security services out of the picture," says Soldatov. "At least, that was the situation before the annexation of Crimea.
"Since then there has been a big change," he adds. "The technological level and scale of cyberactivities has taken a huge leap. The crisis has made it much easier for the Kremlin to mobilize Russians in general, and to approach people in our IT industry for help on an informal basis."
Unlike the US, where there is a large overlap between state and private IT sectors – think Booz Allen Hamilton – Russia's IT industry has taken off in recent years largely without state support, says Tim Bobak, a Moscow-based expert with Group-IB, a cyberthreat intelligence company.
"The Russian IT sector has emerged largely on its own," he says. "It has good professionals. Its main problem is how to export its knowledge. Individuals can leave, but relatively few companies have managed to break out of the Russian market."
Russia, with its great national strengths in maths and engineering, has given the world a great many IT experts – and also populated the criminal underworld with highly qualified hackers. According to a report on cybercrime released this year by Group-IB, "16 out of the 19 trojans most actively used for theft can be linked to Russian-speaking cybercriminals."
A Kremlin connection
How the Kremlin enlists expertise from the private IT sector, and perhaps the criminal world as well, remains murky, says Soldatov.
"We know there is a huge pool of capable talent, and at least some people who are willing to do things that are suggested to them," he says. "We know such things are being done. What we don't know is how or why such orders are formulated, and who exactly may be involved.
"I personally don't think there is a coherent strategy at work, say, to destabilize American democracy. I think there are tactical experiments that are undertaken. When they work, they get people excited. After these hacks against the Democratic Party in the US, people say 'look, they're talking about a third force in the US elections, wow, let's do more of that,' and so on," Soldatov says.
Earlier this year a massive attack, reminiscent of the ones Vyarya described, nearly shut down Ukraine's power grid and demonstrated the extreme vulnerability of public infrastructure.
Hacking and leaking information for political impact has become depressingly commonplace. Many Russians blame US secret services for the Panama Papers last spring, which implicated close friends of Vladimir Putin in financial corruption. This week a group of Ukrainian hackers released scores of email documents allegedly from accounts connected with Vladislav Surkov, a top Kremlin aide, that purport to illustrate Russian plans to destabilize Ukraine.
Cyberbarriers
Ukrainians have the advantage of knowing Russian language and habits, and may be uniquely poised to attack Russian interests. But experts say threatened attempts to retaliate against Moscow from the West may fall flat due not only to the language barrier, but also the higher levels of secrecy common in Russian society and officialdom, as well as a media culture that effectively blocks and dilutes bad news.
"The thing that is most remarkable about the alleged hacks against the DNC and Hillary Clinton's campaign is not the technological expertise of the intrusion, which was not high at all, but the level of social intelligence that was involved," says Soldatov. "You need to know who's who in the Clinton campaign, how the chain of command runs, and an awful lot of background to go in and get the information you want, and correctly evaluate it. This suggests that the simple idea that it was military intelligence, the GRU, or the FSB [Russia's internal spy service] that did these things on their own is not an accurate picture. Outside the former Soviet Union, these agencies are not all that effective."
The relative isolation of Russia in the global IT market may also work to its advantage if it comes to a major cyber-showdown with the US, experts say.
"While we don't yet have independence from foreign-made equipment and operating systems, we are almost completely self-sufficient in cybersecurity systems," says Sergei Sherstobitov, head of Angara IT, a private Moscow-based security firm. [Editor's note: The original version misspelled Mr. Sherstobitov's last name.]
"There is a concerted effort now to correct these deficiencies, and Russia is becoming gradually less and less dependent on Western technology. Everyone is much more aware of the need for cybersecurity than we ever were before."