What US cybersecurity needs: a few more good guys
Loading...
America’s next generation of cyberdefenders did battle recently at the National Collegiate Cyber Defense Competition finals in San Antonio, the Super Bowl of college computer-security tournaments.
The collegians’ assignment: to defend a business computer network with digital defenses as porous as Swiss cheese from a “red team” of professional hackers from the military and federal agencies.
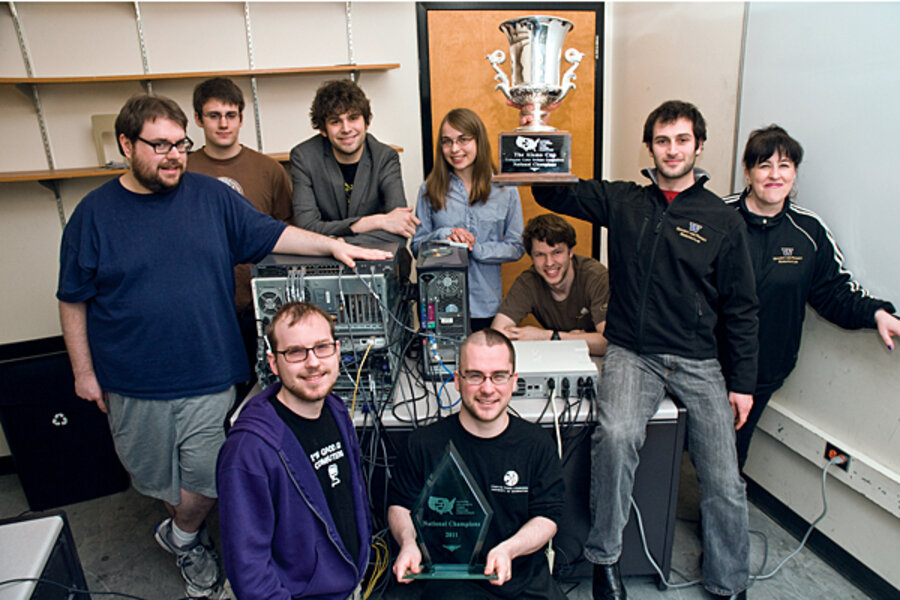
After 17 grueling hours, computer science graduate student Alexei Czeskis and his “cyber swat team” buddies from the University of Washington emerged victorious, slamming their digital doors on the red team’s top guns.
The truth is, America could use several thousand more cyberwarriors just like Mr. Czeskis and his teammates to address an embarrassing national computer glitch: The tech-savvy nation that invented the single-chip microprocessor is weak on cyberdefenses and lacks the “human capital” to protect itself.
What is at risk from the cyberattackers? Anything from corporate crown jewels – critical proprietary data – that can give the owner a competitive advantage to classified data such as weapons designs or national security procedures. In 2008, a foreign intelligence service infiltrated thousands of military computers belonging to the US Central Command – the “worst breach of US military computers in history,” William Lynn, deputy secretary of defense, admitted recently. Just last year, hackers seeking trade secrets hit Google and the networks of dozens of other US companies.
Those attacks are just part of a continuing drumbeat of successful cyberattacks on US government and industry. Even though the United States is believed to lead the world in developing offensive cyberweaponry and espionage capabilities, experts say it lags badly on defense.
“We realized a few years ago that we keep getting whacked and that we just can’t have this anymore,” says James Lewis, a senior fellow at the Center for Strategic and International Studies in Washington and author of a 2010 CSIS report on the nation’s “human capital crisis” in cybersecurity expertise. “People have reassessed the balance of skills needed for national security, for economic security.... There’s a major shortfall.”
“There are about 1,000 security people in the US who have the specialized security skills to operate at world-class levels in cyberspace – we need 10,000 to 30,000,” Jim Gosler, director of the CIA’s Clandestine Information Technol–ogy Office, told CSIS in its report last year.
The FBI is no exception. In a report on April 27, the Department of Justice inspector general found that more than one-third of 36 elite cyberinvestigators in 10 of its 56 bureaus “reported that they lacked the networking and counterintelligence expertise to investigate national security [computer] intrusion cases.”
The federal government, which awoke gradually to the danger during the Bush administration, has accelerated efforts to improve the nation’s defenses. Existing training and education programs are “limited in focus and lack unity of effort,” the cyber education section of President Obama’s Comprehensive National Cybersecurity Initiative found last year. To ensure an adequate pipeline of skilled people “it will take a national strategy, similar to the effort to upgrade science and mathematics education in the 1950s, to meet this challenge.”
Companies and government agencies interested in developing cybersecurity talent are now pushing for more programs in college and tougher curricula.
Colleges and universities like Purdue and Southeast Missouri State are expanding their cybersecurity programs while others are developing entirely new programs, CSIS’s Mr. Lewis says. The University of Maryland University College in Adelphi last year launched undergraduate and graduate programs in cybersecurity – signing up 900 students in both. For UMUC, it makes perfect sense: The cyberskills-intensive National Security Agency headquarters is only a few miles from campus.
A critical part of the problem though is certification and credentialing of experts already on the job. One federal agency recently tested a dozen new employees for cybersecurity skills on their résumés – and got a rude surprise, says Alan Paller, research director of the SANS Institute, a cybersecurity education organization.
“When the dozen new agency employees were confronted with a skills test, three-quarters of them didn’t know what to do,” he says. A credential has to mean a lot more than just knowing when to order an antivirus scan, since the most dangerous, advanced threats are undetectable by them and do not cause system problems. What’s needed are forensic and “hunter skills,” Lewis and Mr. Paller agree.
To fix that problem, a new organization called the National Board of Information Security Examiners based in Idaho Falls, Idaho, is developing tests to ensure its credentials mean an individual has the ability to identify threats on the network.
But it’s not curricula or credentials that will recruit the next generation of cyberdefenders. Competitions might.
The national cyberdefense competition – sponsored by Deloitte, a consulting company – has grown from 24 competing colleges in the 2006 national competition to 109 this year. Others contests like Cyber Security Treasure Hunt, Cyber Patriot, Netwars, and DC3 Digital Forensics challenge are emerging, too.
And then there are the prizes. Beating powerhouses Texas A&M (second place) and University of Louisville (third place) was a sweet victory for Czeskis and his University of Washington teammates. But they won something else even sweeter: Each was deluged with job offers from the likes of Google, Microsoft, and the Department of Defense.