Paris attacks a wake-up call for US intelligence?
Loading...
| Washington
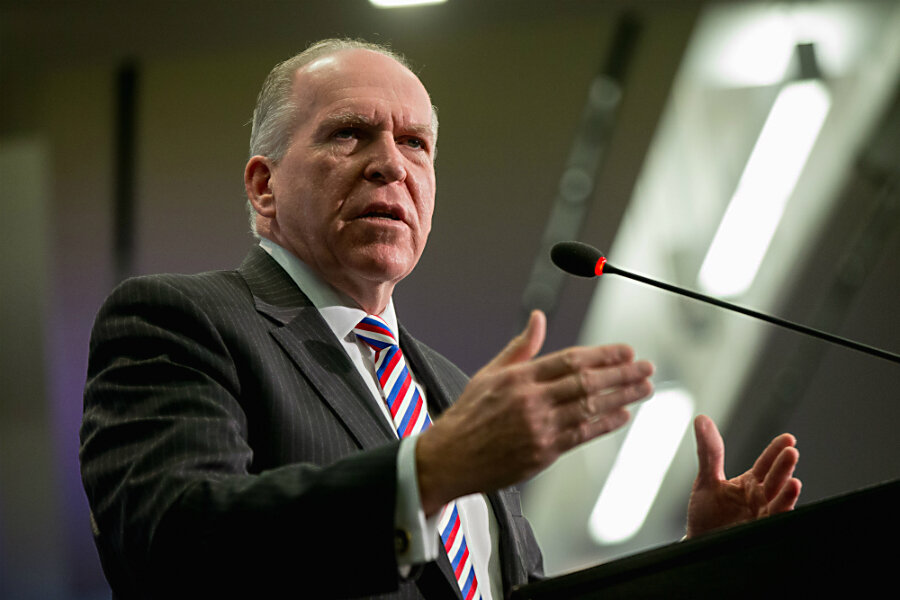
Central Intelligence Agency Director John Brennan appeared to revel in a bit of an “I told you so” moment in the days after the Paris attacks.
Calls for privacy and civil liberties after intelligence leaks by former National Security Agency contractor Edward Snowden created “inadvertent or intentional gaps” in intelligence gathering, he said. That has hampered the ability of United States officials “to protect the people that they are asked to serve.”
“I do hope this is going to be a wake-up call.”
It was an opening salvo in what many argue should become a renewed debate about data collection by America’s intelligence agencies, including the NSA. It is a discussion, Mr. Brennan and others agree, that must involve figuring out how to ensure that the US gets the right balance – or as close to it as possible – between protecting the country from terrorist attacks and protecting the civil liberties of its citizens.
“Security and privacy are certainly not mutually exclusive,” Brennan said in remarks on Nov. 16 at the Center for Strategic and International Studies in Washington.
Events like the Paris attacks tend to lead, in their immediate aftermath, to emotional responses that do not always prioritize civil liberties, analysts point out. In that sense, the French response to the attacks offers a cautionary tale, Matthew Olsen, director of the National Counterterrorism Center from 2011 to 2014, said Monday.
French police, under new state of emergency measures, are now permitted, for the next three months, to conduct warrantless searches of homes and place people under house arrest.
“It’s a worthwhile thought experiment to imagine a Paris-style attack in New York, and imagine how we would react,” Mr. Olsen said in a discussion at the German Marshall Fund in Washington.
It’s a better discussion for Americans to have now, “rather than in a post-attack situation like Paris, where we may miss the mark,” he said.
It is a conversation that must involve some acknowledgement from US intelligence agencies that trust with the American people was broken in the wake of the Snowden leaks. Those leaks occurred after US officials issued public assurances that no such data collection was taking place.
“What’s most troubling about the leaks is that the way that the government had been describing the programs seemed to be intentionally misleading to the American public,” says Paul Scharre, senior fellow at the Center for a New American Security in Washington.
Despite Congress debating some curbs on the government’s bulk collection of Americans’ phone records earlier this year, “I don’t have the sense that after the Snowden revelations we’ve had a very serious, honest accounting about what we’re willing to do, or not do,” Mr. Scharre says.
That may depend in part on the current capabilities of terrorists like those in the Islamic State.
For his part, Brennan said that a number of these operatives and terrorist networks “have gone to school on what it is that they needed to do in order to keep their activities concealed from the authorities.”
However, others say the Snowden fallout hasn't changed much.
For example, the Islamic State was using encrypted apps and websites before the NSA’s surveillance operations were uncovered, John Chase, a cybersecurity specialist who has worked with the hacking group Anonymous, told The Washington Times Friday.
“They were on the dark Web pre-Snowden,” Mr. Chase said, referring to websites whose addresses are not visible to the public, and where cybercrimes tend to take place.
The Snowden leaks, after all, were not the first indication that the government was tracking metadata. Drone strikes alone were enough to persuade many terrorists not to use unencrypted phones, Chase added. US officials often used cellphone tracking to pinpoint their targets.
It is also increasingly hard to determine when an online relationship has actually tipped into an intent to plot a terrorist attack, Olsen said.
Once terrorists are confident they have persuaded adherents to carry out an attack, they urge the adherents to immediately end contact.
Terrorist leaders tell the potential attackers, “Don’t travel anymore, don’t communicate – just carry out a basic attack against a military person [or] law enforcement person, and you’ve fulfilled your duty,” Olsen said.
As a result, it’s “very difficult to say, ‘OK, here’s where we need to target our effort,’ ” he added. “These are troubled souls.” And that’s precisely the challenge from a policy perspective: “How do you stop troubled souls from getting a gun – or a knife?”
One manageable step the US and its allies could take is to improve information sharing, Olsen said. “We know the identity of many of these foreign fighters,” he noted. “We have to make sure the Europeans have it – and that they share it with each other.”