What caused the global 'WannaCry' ransomware attack?
Loading...
| Hong Kong
Experts are trying to figure out who’s behind a global “ransomware” software cyberattack that shut down hundreds of thousands of computers around the world by exploiting a software vulnerability.
Some details about the “WannaCry” attack, which emerged late Friday, and what you can do to stay safe:
HOW THE VIRUS WORKS
Cybersecurity experts say the worm affects computers using Microsoft operating systems and takes advantage of a vulnerability in the software to spread the infection. “WannaCry” is particularly malicious because it takes just one person to click on an infected link or email attachment to cause the virus to spread to other machines on the same network.
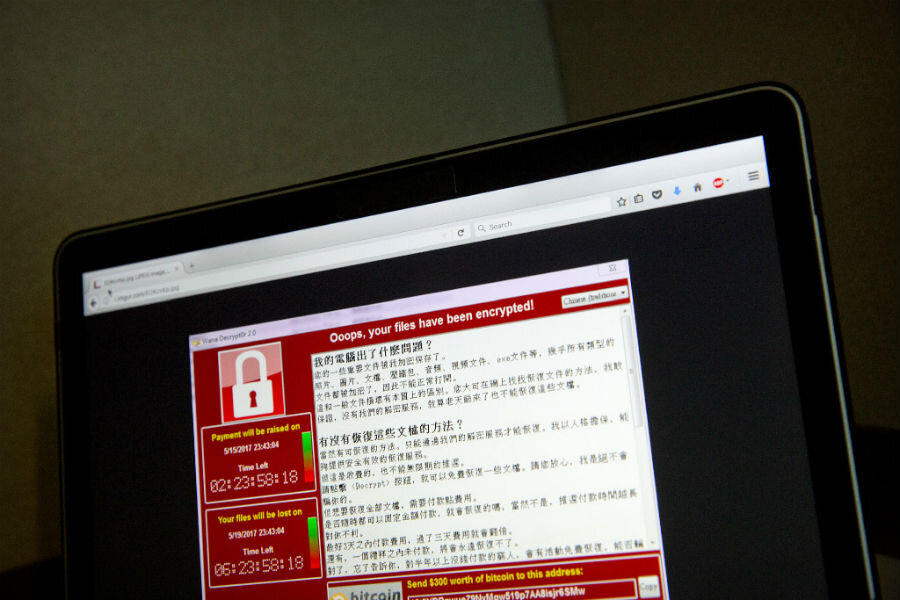
Infected computers are frozen and display a big message in red informing users, “Oops, your files have been encrypted!” and demanding about $300 in online bitcoin payment. Victims have only hours to pay the ransom, which rises to $600 before the files are destroyed.
Money has been trickling in, according to a Twitter account monitoring bitcoin wallets linked to the attacks, with victims paying nearly $39,000 by Monday afternoon in Asia.
THE IMPACT
The worm has claimed at least 200,000 victims since Friday, according to one count by Europol, Europe’s policing agency. Cases have been reported in 150 countries, and include Chinese gas stations, Japanese broadcasters, Indonesian and British hospitals, and German railways.
“We think Asia-Pacific was impacted probably not as heavily as the European regions, but I don’t think they dodged a bullet,” said Tim Wellsmore, Asia-Pacific director for threat intelligence at FireEye, a California-based network security company. He said ransomware attacks are an everyday occurrence, and that victims tend to be small businesses that don’t have as much money to invest in cybersecurity.
Mr. Wellsmore said Asia was likely spared the brunt of the attack because of the timing. “Just as those attacks were picking up speed, we were heading into Friday evening and turning off a lot of computer systems,” he said.
HOW CAN I PROTECT MY PC?
Computer users should patch their machines with updates from Microsoft, especially those using older versions of operating systems such as Windows XP. Microsoft did put out a patch two months ago for more recent systems, but not all users may have downloaded it. After “WannaCry,” it released an emergency patch for older systems too.
RANSOMWARE IS BIG BUSINESS
The “WannaCry” attack grabbed headlines around the world because of its scale, but it’s just one of many types of ransomware that cybersecurity experts see every day. That’s because it’s a very easy way to make money. “It’s a business model that works and you don’t need a lot of investment to actually get a decent return,” said Wellsmore.
“You can buy ransomware kits on the dark web, you can buy all the tool sets you need to undertake your own ransomware campaign quiet easily,” he said, referring to an area of the internet often used for illegal activity. Would-be extortionists can launch a global campaign with little effort, yet authorities can do little because it’s very difficult to investigate, Wellsmore said.
WHO IS BEHIND THE ATTACK?
Wellsmore and other cybersecurity experts say the identity of the perpetrators is still unknown. The hackers were using tools stolen from the U.S. National Security Agency and released on the internet. The software vulnerability was purportedly first identified by the NSA for its own intelligence-gathering work.
“We don’t expect this to be a sophisticated group,” said Wellsmore. “We expect this is a small operation that is undertaking this. They just happen to hit the motherlode. Unfortunately for the rest of us, this thing went quite global quite quickly.”