Did Iran hijack the 'beast'? US experts cautious about bold claims.
Loading...
An Iranian claim that it used cyberwarfare techniques to hijack a US stealth drone, getting it to land in that country, drew deep skepticism from some US cyberwarfare experts who doubt Iran's ability to carry out such an operation.
Iran gained control of the drone by overwhelming the GPS signal that was guiding the aircraft with an Iranian signal, an Iranian engineer told The Christian Science Monitor on condition of anonymity. An Iranian cyberwarfare team then made the drone believe it had arrived home and should land, the source told the Monitor.
To accomplish such a cyber coup, at least three and probably many more major technical hurdles would need to be overcome, several US cyberwarfare and drone experts said. While none of these steps is impossible, each is difficult, and taken together, they represent a massive technological challenge for any enemy hacker – one that the US experts suggest is beyond Iran’s capabilities.
On one hand, hacking into drones is not unprecedented. Speculation persists that Iran-backed Hezbollah has successfully crashed Israeli drones. Moreover, in 2009, Iraqi militants using off-the-shelf software broke through safeguards to download live, unencrypted video from US drones.
Even in the US, a computer virus infected the virtual cockpits of pilots controlling America’s Predator and Reaper drones at Creech Air Force Base, Nev., "logging pilots’ every keystroke as they remotely fly missions over Afghanistan and other warzones," Wired.com reported in October.
But the hijacking and safe landing of the RQ-170 in Iran, if true, would represent a new level of cyberintrigue in the drone wars.
First, Iran would need to spot the stealth drone. Second, it would need to jam the encrypted GPS signal. Third, it would have to substitute a false signal that the internal systems on the drone could understand and obey.
US experts say even the first task – spotting the drone – would be very difficult for Iran.
"The weak point in the Iranian argument is how they detected the drone in the first place, which I find implausible given the existing quality of their air-defense system, which is not sufficiently sophisticated to detect it," says Dennis Gormley, a University of Pittsburgh expert on unmanned air systems, including cruise missiles and drones, who also worked in the intelligence community. "Their air defenses are of a type that doesn't have the ability to detect a low-cross-section vehicle like the RQ-170."
Locating a stealth drone operating at perhaps 40,000 feet would stretch even Russia and China, which have far more sophisticated radar defense systems, he says.
Aviation website AviationIntel.com, however, notes that Iran recently took possession of an advanced jamming system from Russia called “Avtobaza” that perhaps could have detected communication signals going to and from the drone.
"There is no reason why [that] system could not have detected the Sentinel's electronic trail and … jammed it," the site reads.
US experts are unmoved. The US used a stealth helicopter in the Osama bin Laden raid that went undetected, and US military planes have bombed all over the world undetected. So for Iran to detect a far-smaller stealth drone seems "almost like science fiction," says John Bumgarner, chief technology officer for the US Cyber Consequences Unit, a nonprofit cyber-warfare think tank.
Provided that Iran was indeed able to pinpoint the drone overhead, the next step – jamming the GPS signal – might have been comparatively easier, US experts say.
"We have known about the weakness of GPS signals since we invented the system," says retired Air Force Lt. Gen. Harry Raduege Jr., now chairman of the Deloitte Center for Cyber Innovation. "This is not like a surprise or revelation to us."
But he and others say jamming at such high altitudes is no easy feat. Iran would have to have a very sophisticated electronic-warfare group to identify and continuously jam an encrypted signal between a drone and the satellite – and it would have to have been jammed for a long time at high altitudes, they say.
The toughest trick, though, would come in the third step: commanding the drone to land in Iran. Even if Iran managed to jam the drone’s communications, the drone would have gone on autopilot, retracing its steps back to the Afghan base from which it took off. To override this function, the Iranian team would have had to offer fresh commands.
"The problem is that the GPS signals used for this bird are encrypted, which creates a whole level of complexity to take it over," says Mr. Bumgarner.
The Iranian engineer said his team accomplished this by making the hack as simple as possible. The team found a location in Iran that shared the same altitude as the Afghan base, as well as one of the same landing axes (longitude or latitude). That means the team only needed to change one axis to have the drone land in Iran. He said Iran used information gleaned from the capture or shooting down of several nonstealth drones in recent years, which have similar navigation systems.
A new Air Force report from April, leaked this week, also indicates serious vulnerabilities and ways to hack into and "spoof" encrypted military GPS systems.
But US experts' questions remain about whether Iran could do any of this. "They would have to have some kind of software to take control of the craft – to produce signals compatible with the internal software on the drone," Bumgarner says. "I don't think the Iranians have the capability to identify a stealth aircraft on radar, especially a US stealth aircraft, or jam an encrypted frequency used on this bird, or have the software to control the bird."
General Raduege called the encryption hack, in particular, "just Buck Rogers stuff."
One cyberwarfare expert says it might have been possible for the Iranians to cyberjack the drone – but only if they got help from Russia or China. Both nations have world-class cyberwarfare expertise and "may be projecting their own intentions" by helping the Iranians on this, writes James Lewis, director of the Technology and Public Policy Program at the Center for Strategic and International Studies in Washington in an e-mail interview.
Russia, he notes:
- Has focused on beating GPS guidance systems since since the war in the Balkans.
- Monitors US telephone and computer networks (and some radio frequencies) and so could have overheard the Department of Defence discussing drone-related problems.
- Helped the Iranian nuclear program – so why not electronic warfare? Especially since the drone would be a good prize.
The actual encryption on the drone developed by the US National Security Agency would be hard to beat, he writes. But perhaps the Iranians – with the Russians' help – found that there was a vulnerability in how the encryption was applied to the drone's control systems, allowing them to work around it.
Still, most experts consider it more likely that the drone failed for mechanical or other reasons and glided to a rough landing. Experts also question why Iran would divulge how it accomplished such an important technological feat.
"If you had that kind of capability you would not want to reveal it," adds Raduege. "That's why I think this is more about showing off how high-tech we are to take control of a US asset. It's false claims and wishful thinking."
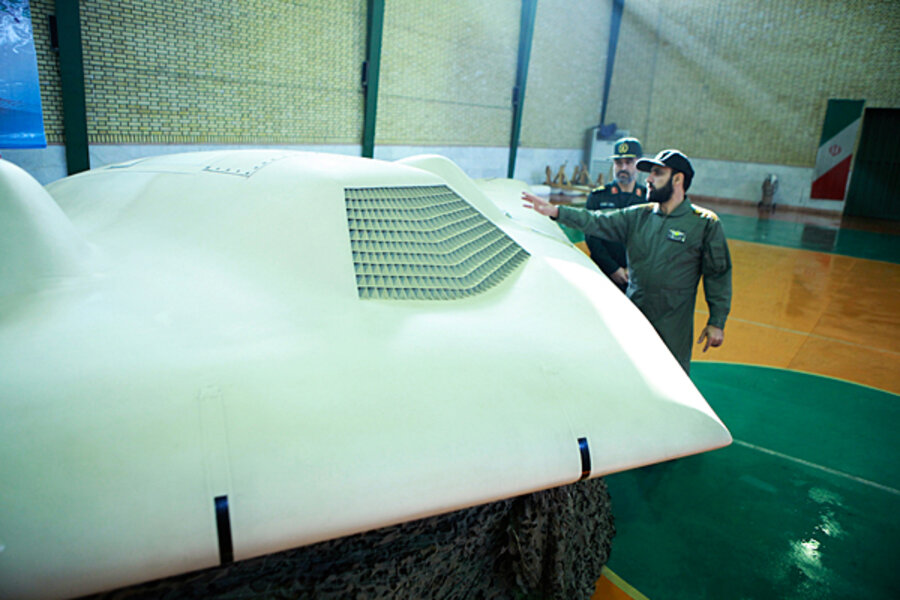
Iran refutes the mechanical-failure theory by arguing that the drone, which is still largely intact, would have suffered more damage from a rough landing – although several experts noted that the landing gear has been obscured, suggesting precisely this sort of damage. Meanwhile, the information on the alleged Iran hack was not made public but rather was uncovered in a Monitor investigation in which the source was initially unaware that the material would be published.
Regardless of who is right, the incident points to important cyber lessons, experts say.
"There's no question that cybercommunications systems on the battlefield will have to get better in the long run," says David Aitel, president of Immunity Inc., a Miami-based cybersecurity company that specializes in offensive cybersoftware. As more drones enter the battlefield, a fleet of drones would have to "talk to each other" in ways that can't be disrupted by the enemy.
You don't want a weapons-laden drone taken over and shooting at friendly troops or targets like a friendly embassy, he notes.
"Friendly fire or firing on a politically important target like an embassy is a nightmare scenario," Mr. Aitel says. "Having it land, that's bad. But not as bad as it could be."